Know
CEO of Clearwater cyber firm is target of ID theft

Stu Sjouwerman, CEO of cybersecurity training firm KnowBe4, found himself on the wrong end of an identity theft scheme over the past couple of weeks.
Someone applied for a Small Business Administration loan in his name, using his social security number. Someone filed for an unemployment claim in his name, again with the correct social security number. And someone created a bogus Facebook account in his name and started contacting KnowBe4 employees.
Sjouwerman is one of 10 million to 11 million Americans every year who are targeted by identity thieves. Although this attack is the first time it’s happened to Sjourwerman — at least the first time he knows of — he’s a cybersecurity expert so he had taken steps to protect himself before it occurred, including freezing his credit records.
“I’ve got my stuff locked down, so I’m assuming I will not be a victim but I’m certainly being attacked,” Sjouwerman said.
Sjouwerman suspects the attacker got personal information about him by purchasing it on the dark web, a subset of the internet that requires special software to access.
“It’s highly likely from data breaches for sale on the dark web. They select victims based on demographics, net worth and that sort of stuff. It’s not hard to combine six or seven data breaches and then sort and slice and dice come up with people who are good candidates for identity theft,” Sjouwerman said.
Sjouwerman came forward with his personal story in a blog post Tuesday. He wanted to send a message. If a cybersecurity expert can be hacked, so can you.
“There are so many data breaches that the personal information of each American is out there on the dark web five times over. That’s not something you can prevent,” he said. “What you can prevent is the actual identity theft in creating accounts in your name. You have to go to the three credit bureaus and take the time and effort to freeze your credit records, and only open them for 24 hours if you really need to, for instance for a car loan. … and then close them again.”
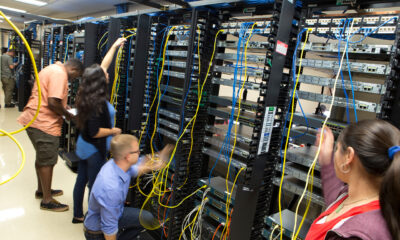
KnowBe4 trains employees to be human firewalls for attempted cyberattacks on their companies. They are taught to be on the lookout for phishing schemes, such as a bogus email from some claiming to be a corporate executive who needs proprietary information or is asking for a password.
There were a couple of warnings in Sjouwerman’s case that he was being attacked. A sharp SBA representative called him to verify the loan request information and he congratulated them for a “good fraud catch.”
In the case of the unemployment claim, there was little chance for success, “since these requests need to be verified by the company in question and KnowBe4 has not laid me off yet,” Sjourwerman wrote in the blog post.
The wording of the fake Facebook account was another tipoff. Although the Facebook post had Sjouwerman’s picture, the Fake Stu lives in Kampala, Uganda — someplace Sjouwerman said he’s never been — and used language that is not the way Sjouwerman talks.

Facebook’s support team took down the phony profile and said they are reviewing the posting.
Sjouwerman described the scheme as the “modern-day clumsy equivalent of the Nigerian 419 scam.” He also advised people to be careful what they post on social media, as it will stay online forever.
Bad guys, or hackers, take the road of least resistance, Sjouwerman said. “It takes three minutes to hack a human. It takes three weeks to hack software. It takes three months to hack hardware. So guess what they do?”
KnowBe4 itself was spoofed last week, when it got emails from users saying its training notifications were being used as click bait for a phishing campaign. The company speculated the spoofed emails were an attempt to get employee credentials for Microsoft Outlook.
“If nothing else, this particular phish should serve as a reminder that no online company or brand is immune or impervious to being spoofed as part of a malicious email campaign. Online brands, sites, and services are all vulnerable to such attacks, and your users should be completely aware of this phenomenon,” a KnowBe4 blog post said.







Mike Manning
September 16, 2020at7:35 am
Freezing credit records at the three credit bureaus isn’t difficult. If need arises to unfreeze your records, that is also easy. Remember that you must unfreeze at all three bureaus and open for a finite time period, like 24 hours.